Nmap (Network Mapper) is a powerful open-source network scanning tool used for network discovery and security auditing. Here are ten commonly used Nmap commands to start with :
Basic Scan (TCP SYN Scan):
- This command performs a basic TCP SYN scan to identify open ports on a target system.
nmap -sS target_ipTCP Connect Scan :
- This command uses a full TCP connection to check if a port is open or closed.
nmap -sT target_ipUDP Scan:
- Use this command to perform a UDP scan to identify open UDP ports.
nmap -sU target_ipOS Detection:
- Nmap can attempt to identify the operating system running on the target.
nmap -O target_ipService Version Detection: - This command detects the version of services running on open ports.
nmap -sV target_ipAggressive Scan:
- This command combines various scan techniques and is more intrusive.
nmap -A target_ipScript Scanning:
- Nmap can run scripts to perform advanced tasks such as vulnerability scanning.
nmap -sC target_ipPing Scan:
- Use this command to perform a simple ping sweep to identify live hosts.
nmap -sn target_subnetFast Scan:
- This command performs a quick scan by skipping host discovery and only scanning specified ports.
nmap -F target_ipCustom Port Range Scan:
- You can specify a custom range of ports to scan using this command.
nmap -p 80,443,8080 target_ip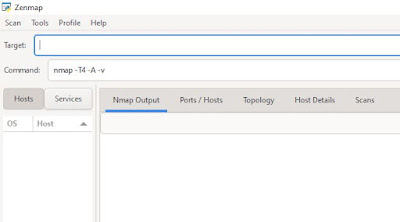
Comments
Post a Comment